With SSO (Single Sign-On), you can sign into your Ada dashboard using your organization’s authentication tool, rather than having to type in your username and password every time you log in.
Setting up SSO requires work at different stages for both your Ada representative and your organization. Your Ada representative sets up Ada’s Okta account to work with your organization’s identity provider (IDP), and you set up your organization’s IDP. Once you have completed this process, you can use the same IDP for multiple Ada instances.
Ada uses Okta as a service provider (SP), but that does not mean you have to use Okta for your organization’s identity provider (IDP).
SSO has the following limitations:
SSO simplifies authentication and strengthens security for your team.
SSO integration supports the following:
email, firstName, and lastName attributes from your IDP to Ada.Set up SSO for your organization in a few steps.
For detailed instructions, see Implementation & usage.
Set up SSO by coordinating with your Ada representative and configuring your organization’s identity provider.
Configure your IDP to work with Ada’s Okta instance.
To set up SSO:
Contact your Ada representative so they can start setting up your IDP in Ada’s Okta instance.
They provide you with two values:
ACS URLAudience URIYou need these values when you configure your SAML application in the next step.
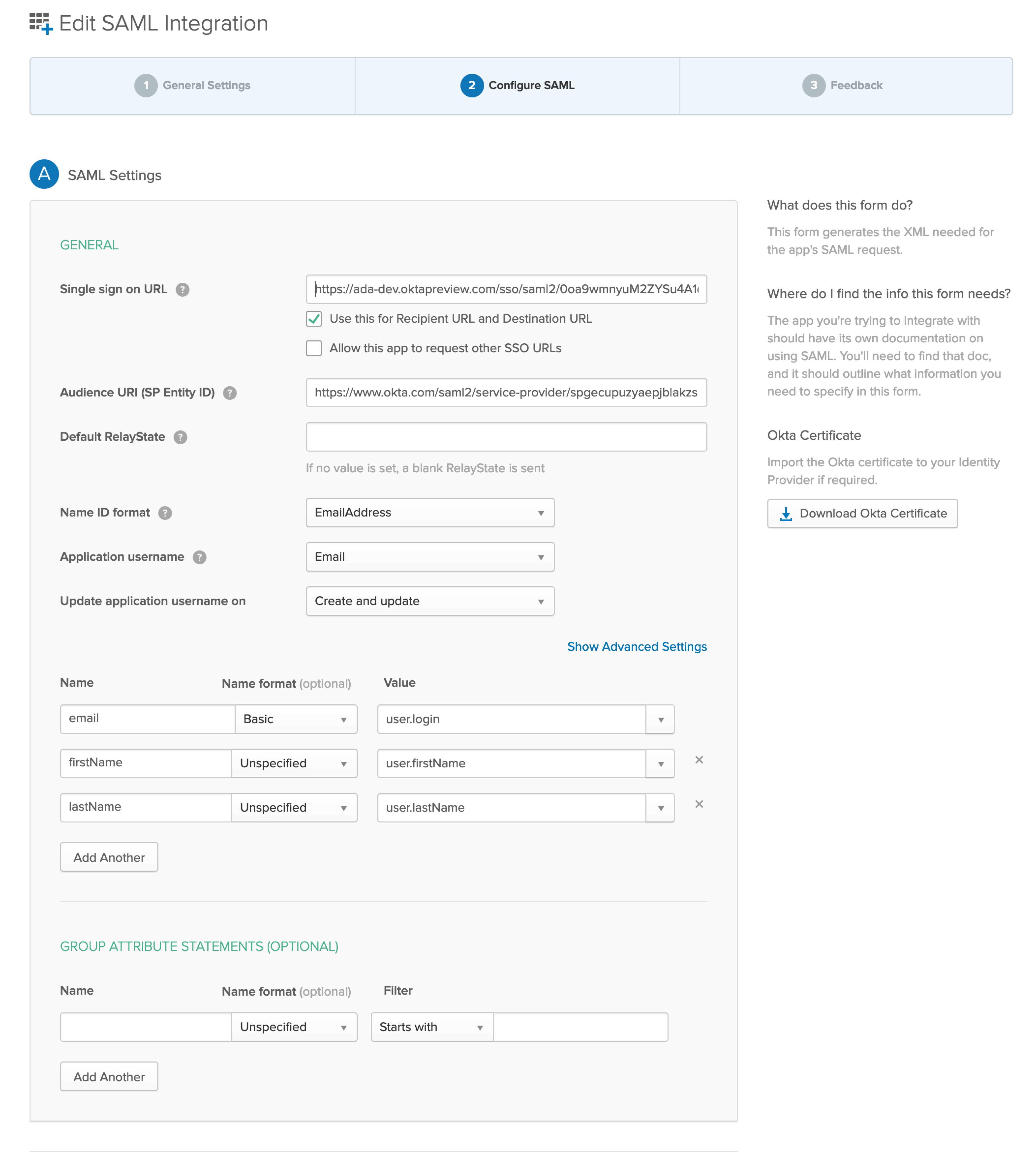
Create a SAML application in your IDP for Ada. Then, configure your SAML application with the following:
Assertion Consumer Service URL (aka Single Sign-On URL): Use the ACS URL your Ada representative provided. The Recipient URL should also use the same ACS URL.
Entity ID (aka Audience URI): Use the Audience URI your Ada representative provided.
Name ID format: email
Application Username: email
Add three more user attributes in addition to Name ID: email, firstName, and lastName
This example shows a completed SAML application configuration in Okta. Note that there is also a button to download a certificate, which you need in step 4. Different tools make the certificate available in different places.
Find your IDP’s metadata. Different IDPs make this information available in different places.
As an example, this is how you can find the metadata in Okta:

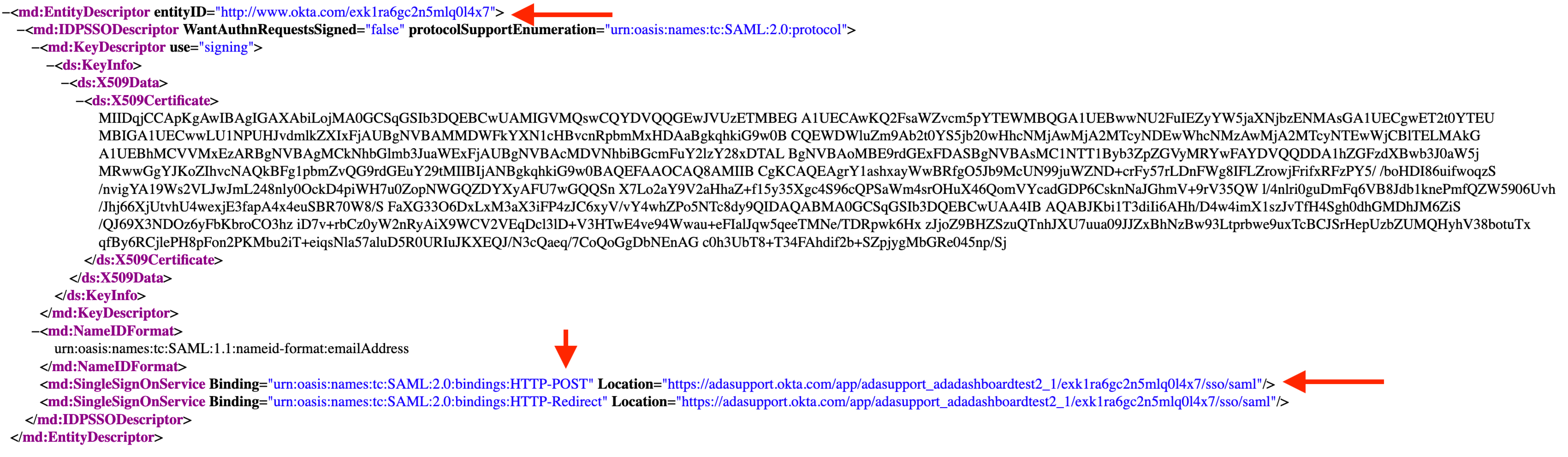
In the metadata, find these two values:
entityIDSingle Sign-On URLSome IDPs have different names for these values. The most reliable way to find them is to find an IDP Metadata .xml file. That file contains these values in a standardized format.
This is how they might look in the .xml file. The Single Sign-On URL is listed as the Location of the SingleSignOnService for HTTP-POST:
Find your IDP’s certificate, which should come in the form of a .crt, .cert, or .pem file.
If you find a string that looks like this, paste it into a text editor and save it with a .pem file extension:
Send your Ada representative the entityID and Single Sign-On URL values and certificate from your IDP.
They can then complete the setup process on their end.
To allow users to log in with SSO, assign them the Ada Support app in your IDP. Then, in your Ada dashboard, delete their existing accounts and add them again, selecting SSO as their login type.
For more information, see Manage users and permissions.
Explore additional access and security options.